Security and Privacy Threats for Bluetooth Low Energy in IoT and Wearable Devices: A Comprehensive Survey

Amazon.com: CME WIDI Jack + DIN-5 MIDI Cable Pack - Bluetooth MIDI Interface with 5-PIN DIN MIDI cables Included - Works with all DIN-5 MIDI devices - Wireless MIDI for Synth Keytar

Amazon.com: NEXAS NexLink Bluetooth 5.0 OBD2 Scanner,Wireless Compatible with Third-Party Apps,Car & Motorcycle Universal Code Reader Check Engine Fault OBDII Adapter Scan Tool for iPhone, Android & Windows : Automotive
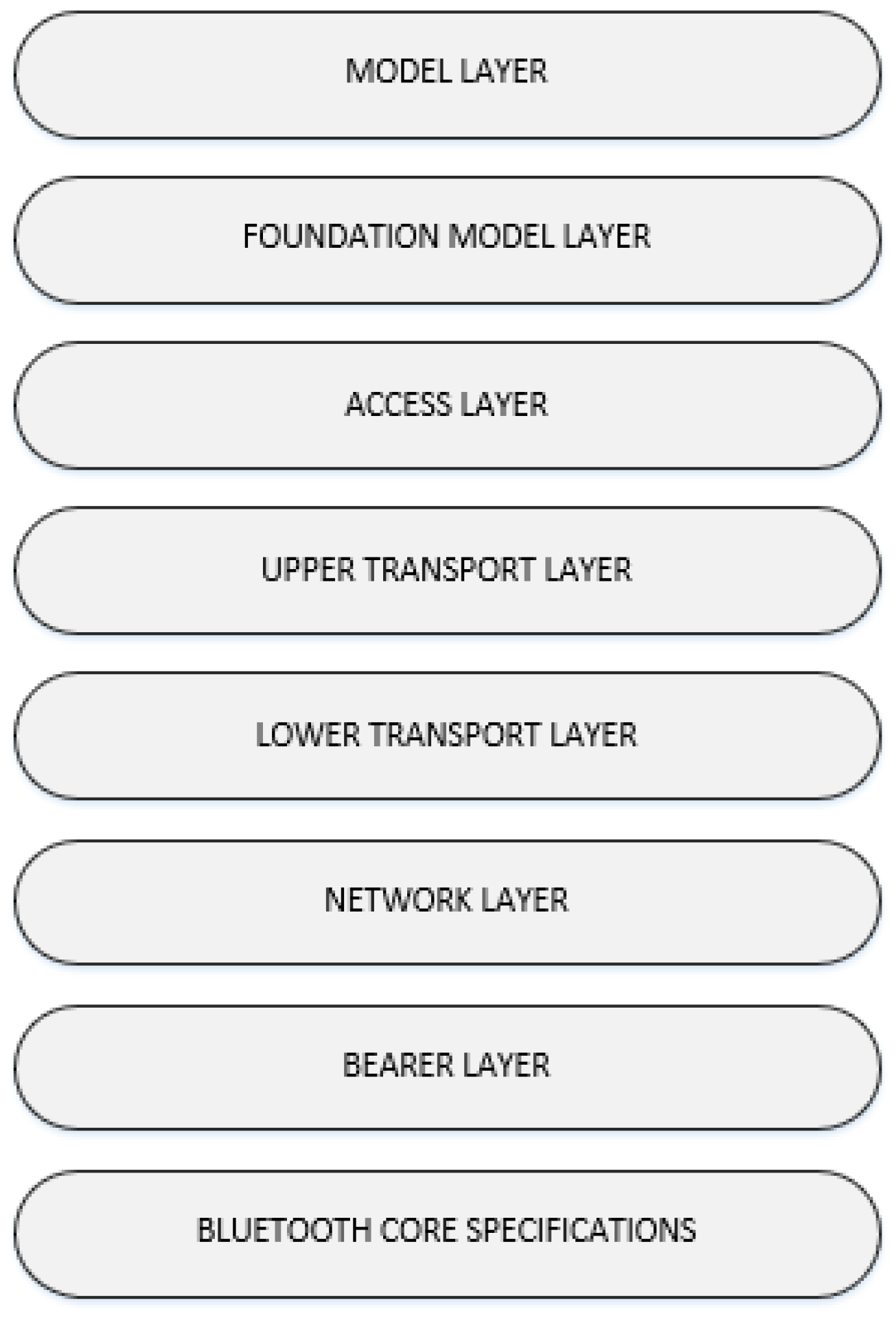
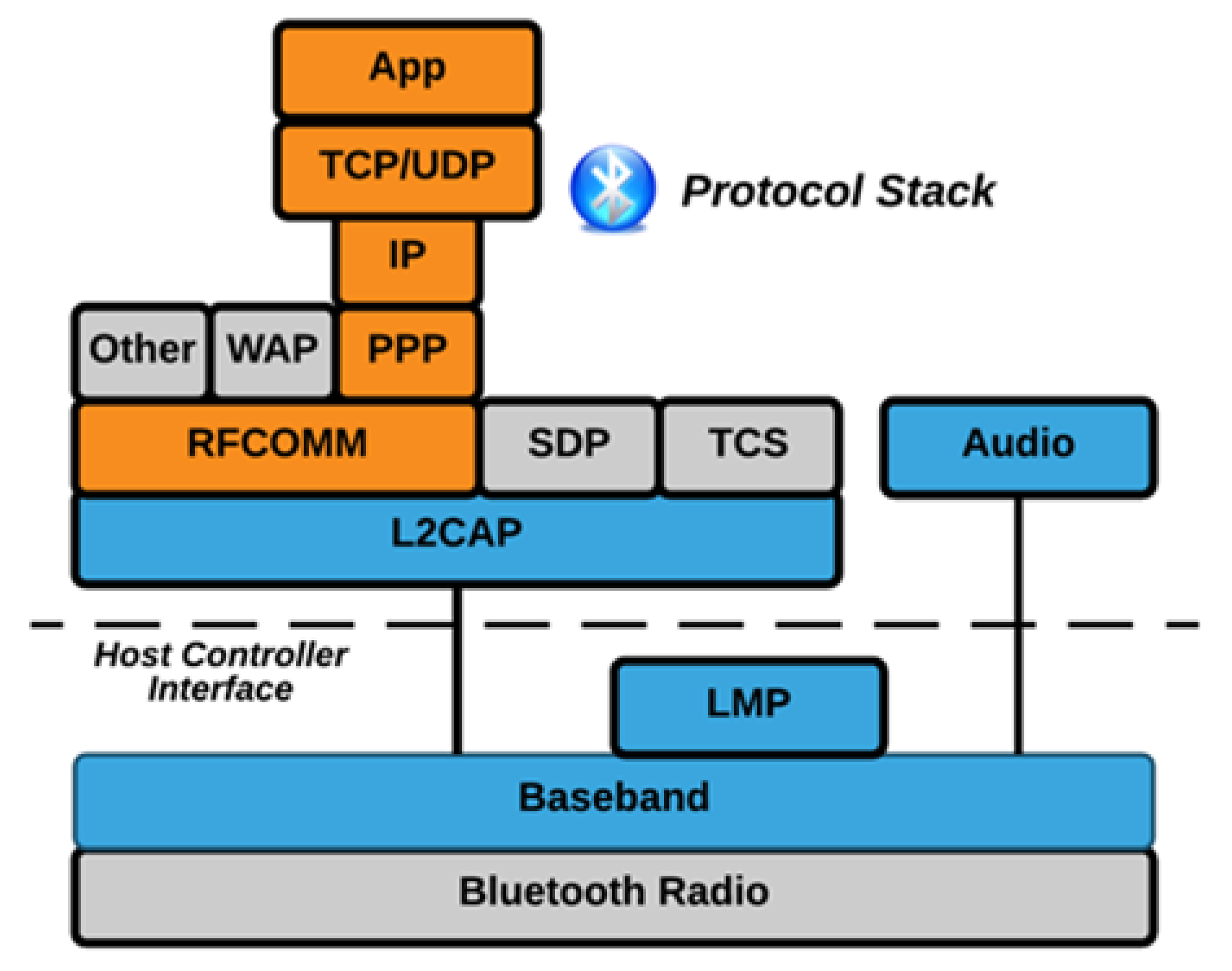
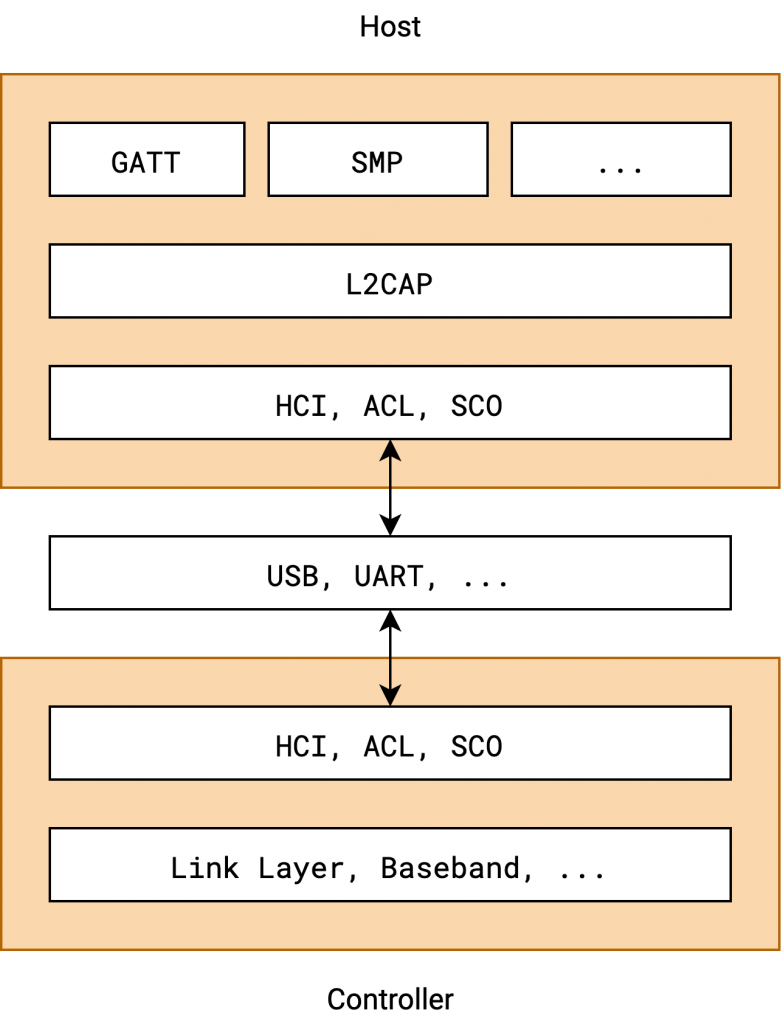
Sensors | Free Full-Text | Bluetooth Low Energy Mesh Networks: Survey of Communication and Security Protocols
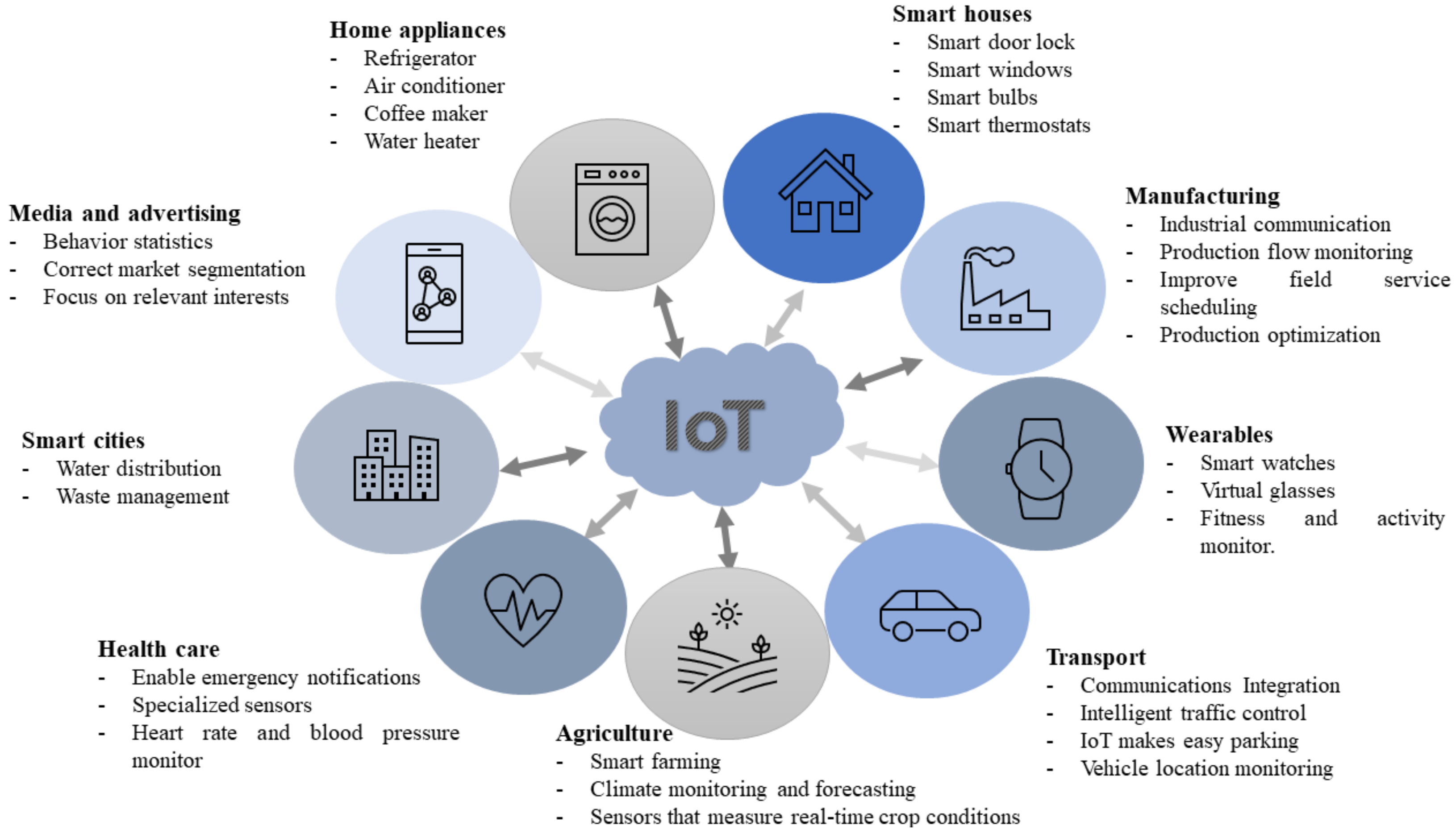
Security and Privacy Threats for Bluetooth Low Energy in IoT and Wearable Devices: A Comprehensive Survey
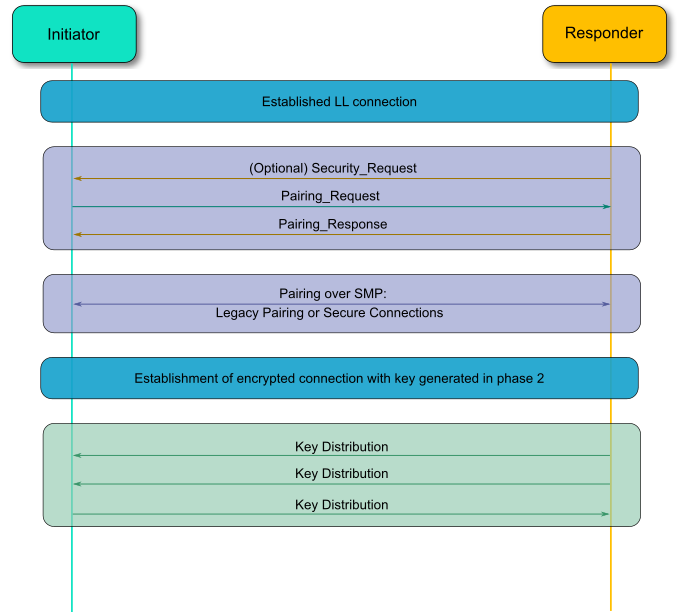
Security and Privacy Threats for Bluetooth Low Energy in IoT and Wearable Devices: A Comprehensive Survey
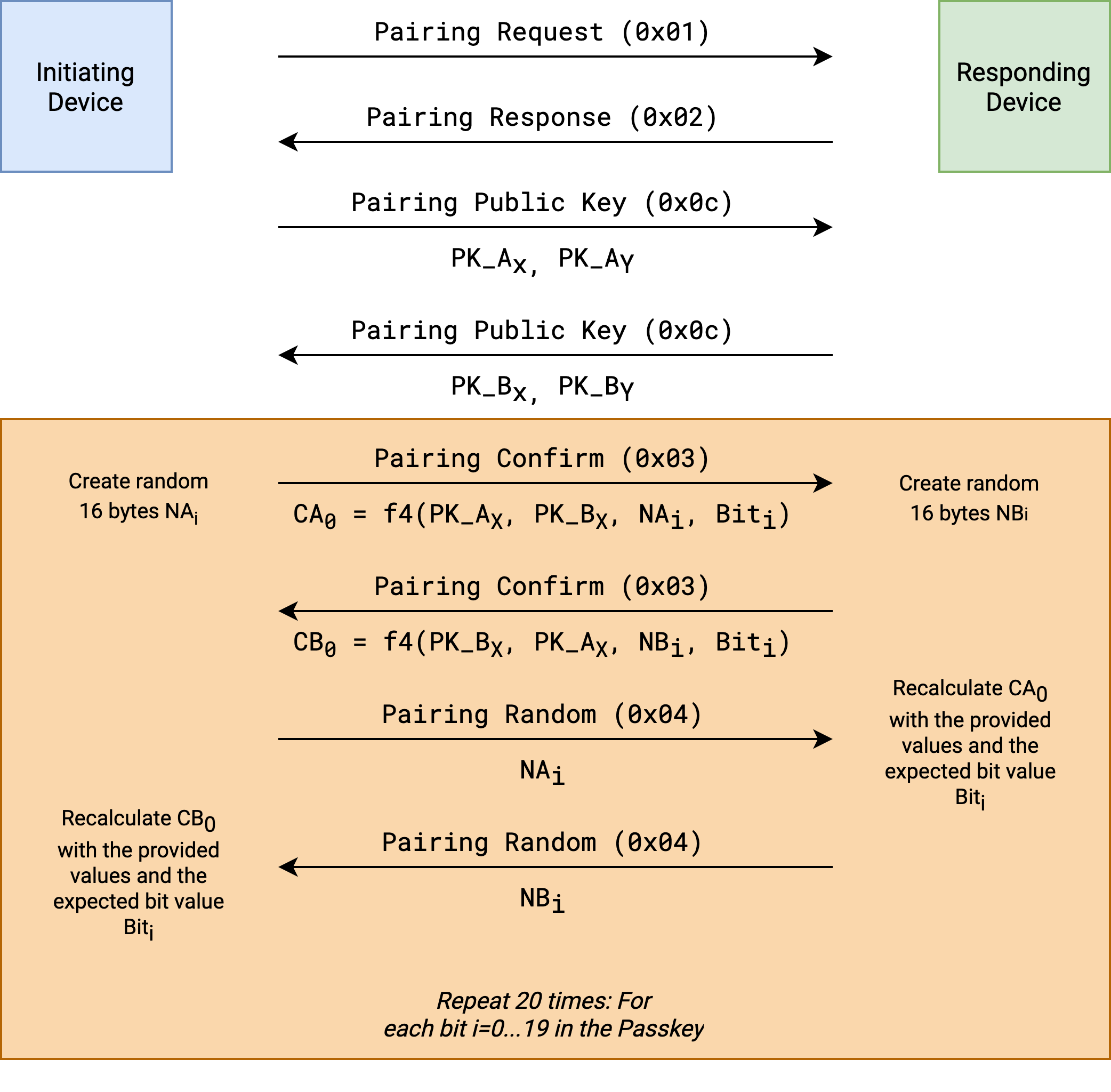
Security and Privacy Threats for Bluetooth Low Energy in IoT and Wearable Devices: A Comprehensive Survey
Security and Privacy Threats for Bluetooth Low Energy in IoT and Wearable Devices: A Comprehensive Survey

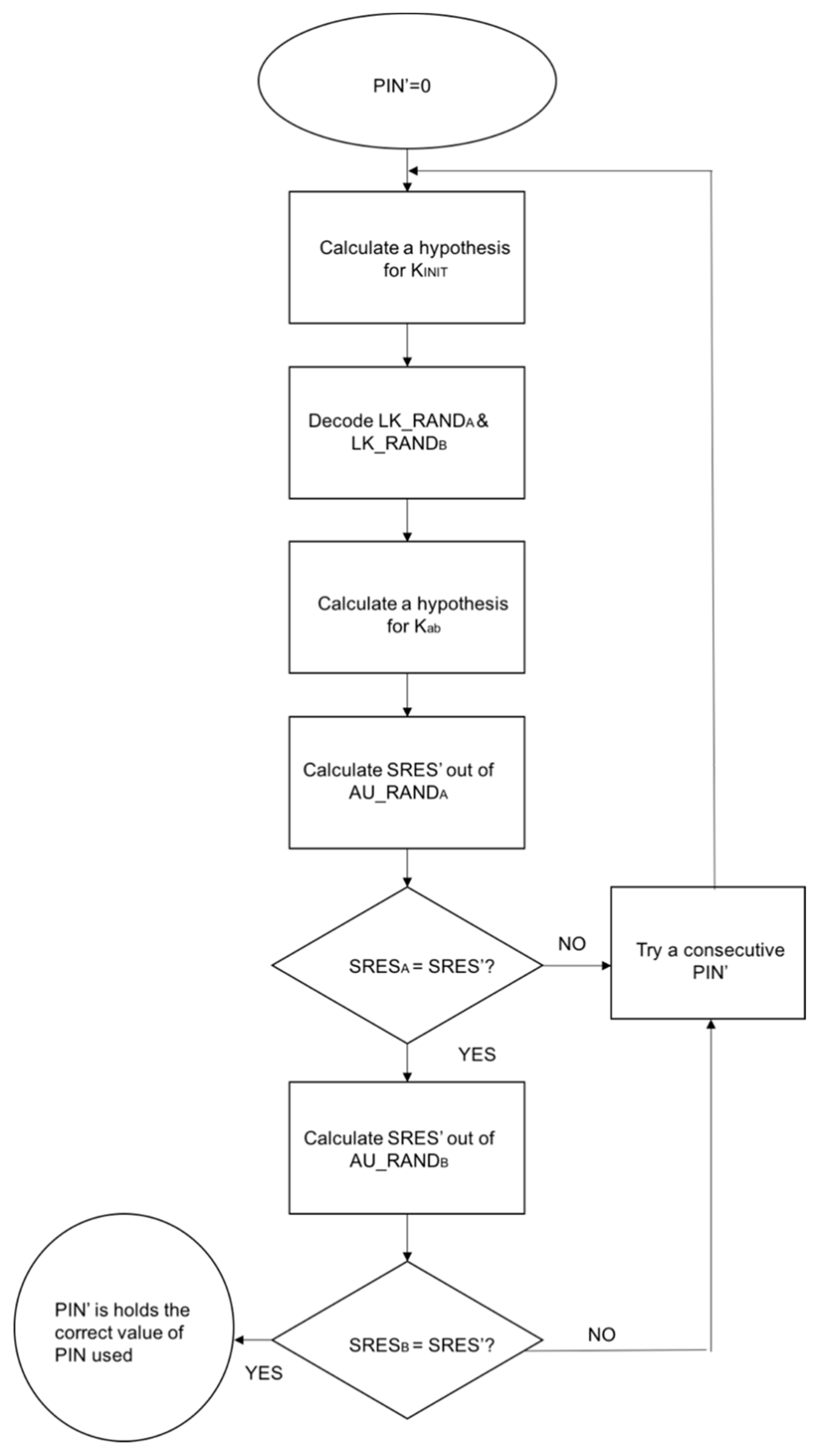



![PDF] Cracking the Bluetooth PIN | Semantic Scholar PDF] Cracking the Bluetooth PIN | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/cf0365e04e863571b5ebbeba4e38c9a333fc38cb/4-Figure3-1.png)




![PDF] Cracking the Bluetooth PIN | Semantic Scholar PDF] Cracking the Bluetooth PIN | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/cf0365e04e863571b5ebbeba4e38c9a333fc38cb/12-Figure12-1.png)